Managed Cyber Security
Cyber Solutions for Business
Several organisations are targeted by hackers on a daily basis, don’t let your organisation be the next, preventing this is key!
✔ One organisation in the UK is successfully hacked every 19 seconds.
✔ Up to 88% of UK companies have suffered breaches in the last 12 months.
✔ One in every 3,722 emails in the UK is a phishing attempt.
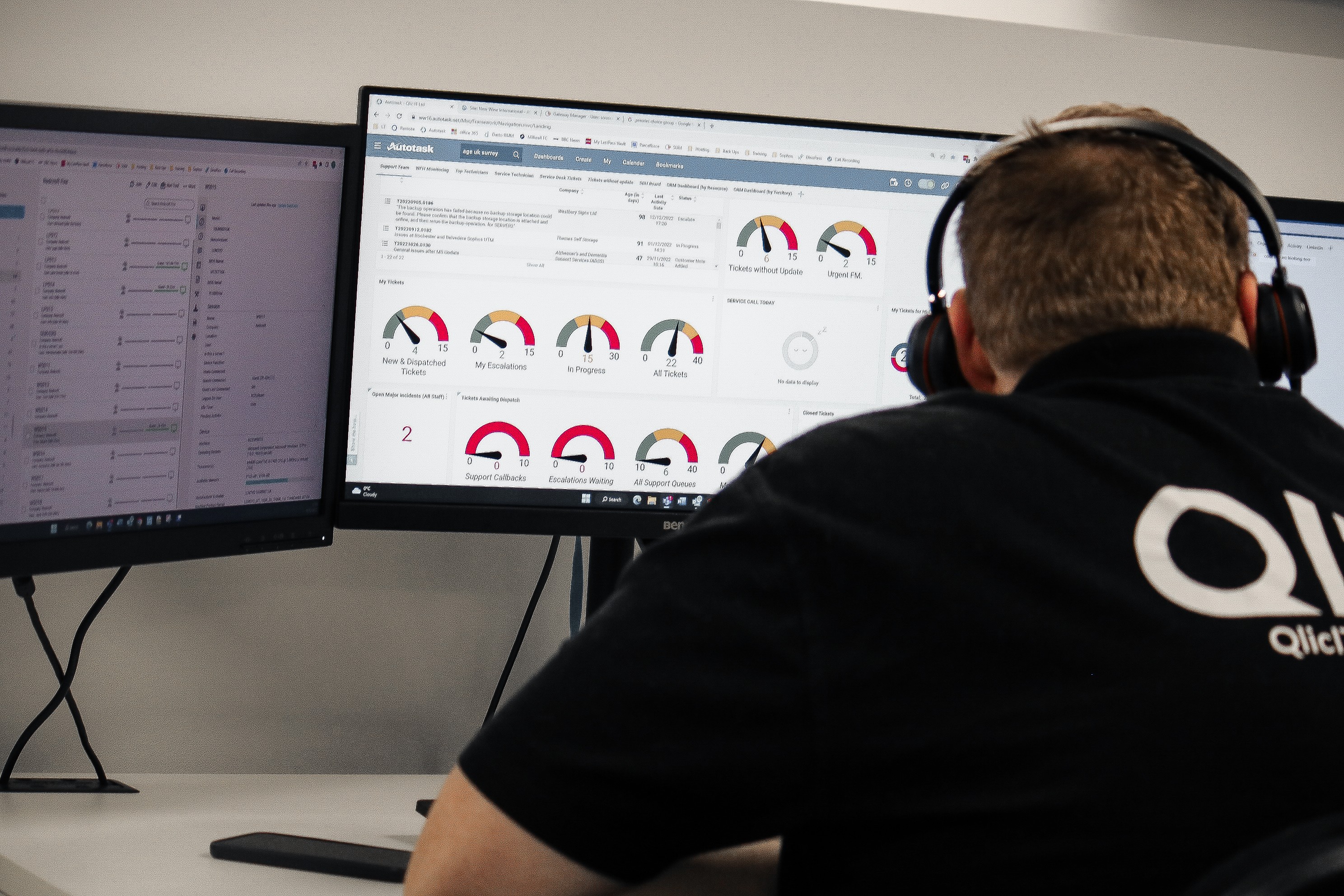
Bespoke Security Solutions
Qlic has a variety of managed cyber security packages that can be tailored to suit your business needs. It is important to review and consider your current data protection capabilities. Having at least the minimum requirements in place is best practice to protect your business against viruses, malware and data leakage
Sophos Managed Detection & Response (MDR)
Sophos Managed Detection & Response provides 24/7 threat hunting, detection, and response capabilities delivered by an expert team as a fully-managed service. MDR leverages multiple technologies and services to detect and respond to threats quickly. These include sensors and analytics that can identify anomalous behaviours or malicious activities; malware detection solutions; incident response plans; and response mechanisms for any identified threats.
Find out more about Sophos Managed Detection & Response (MDR)
Anti-Virus & Malware Protection
Sophos Central Endpoint Protection blocks malware and infections by identifying and preventing the handful of techniques and behaviours used in almost every exploit. Endpoint Protection doesn’t rely on signatures to catch malware, which means it catches zero-day threats without adversely affecting the performance of your device. So, you get protection before those exploits even arrive.
Email Filtering
With Microsoft 365 Advanced Threat Protection, you can protect your cloud mailboxes against new, sophisticated attacks in real time. By protecting against unsafe attachments and expanding protection against malicious links, it provides advanced security features to provide better zero-day protection.
Find out more about Microsoft 365 Advanced Threat Protection (MDR)
Ransomware Protection
Ransomware is the number one cyber attack affecting organisations today. It encrypts your files and holds them hostage until the ransom is paid, causing massive disruption to your charity’s productivity. Sophos Intercept X features CryptoGuard, which prevents the malicious spontaneous encryption of data by ransomware—even trusted files that have been hijacked.
Device Encryption
Each year, millions of laptop computers are misplaced, stolen, or lost; many of them containing important and sensitive data. Full disk encryption is the essential first line of defence to protect your data in any of these events. Sophos Central Device Encryption gives you the ability to manage full disk encryption from a single, integrated, web-based management centre.
Enterprise Grade Firewall
Sophos XGS provides the ultimate network security package with everything you need in a single modular appliance. It simplifies your IT security without the complexity of multiple-point solutions. The intuitive interface will help you quickly create policies to control security risks. And clear, detailed reports will give you the insight you need to improve your network performance and protection.
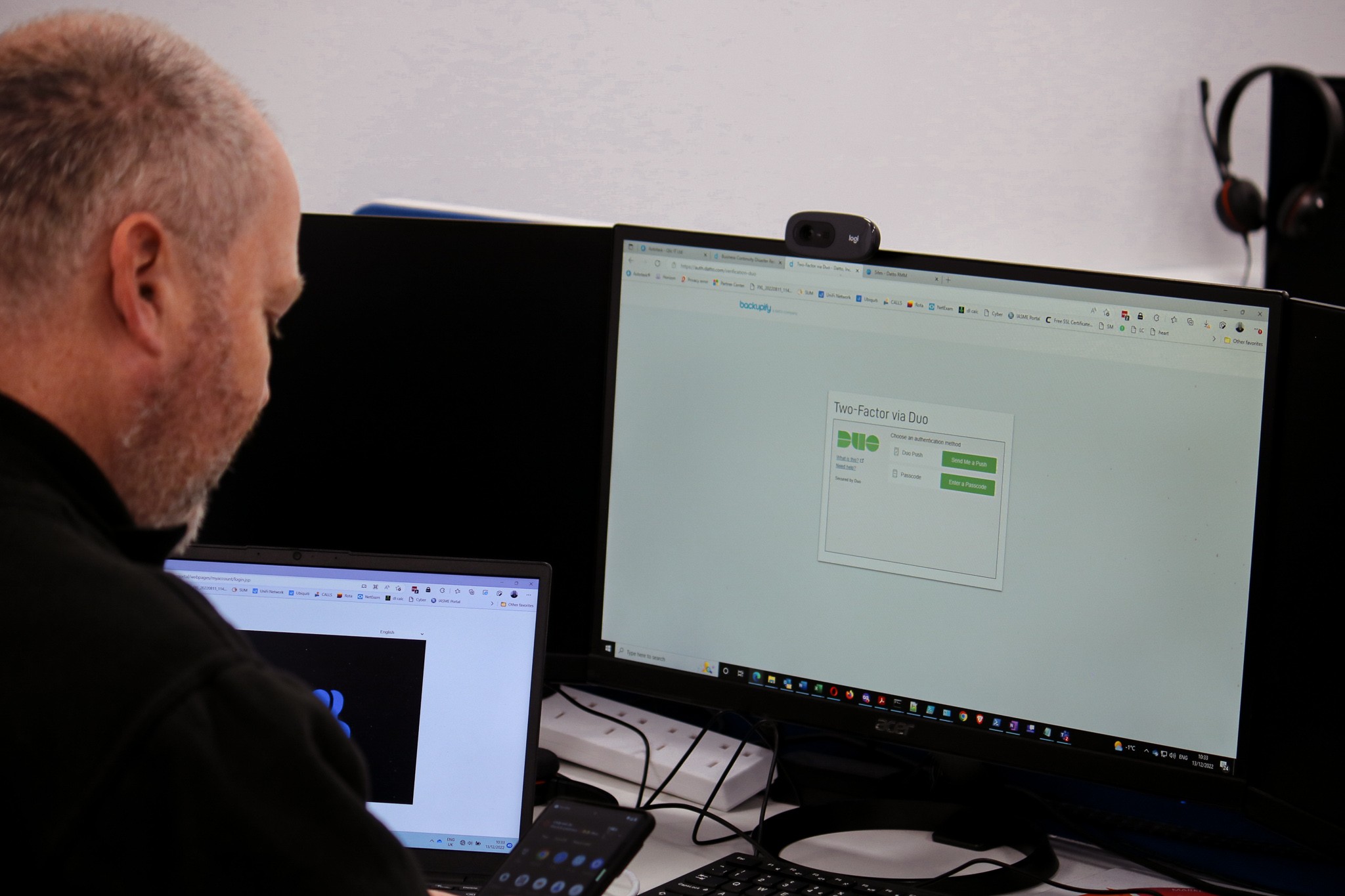
Multi-Factor Authentication
Protect your network using multi-layered proven protection technologies. Multi-Factor Authentication is an easy-to-use, secure authentication solution to verify your user’s identity when logging into any account..

Download Our Cyber Security Brochure
Cyber Essentials

As a Cyber Essentials certified organisation ourselves, Qlic is very familiar with the process of accreditation. We have supported many organisations through the process and implemented any necessary changes needed to achieve their own certifications.
With cyber security becoming a vital part of any project we also ensure that all new projects are Cyber Essentials certified, giving your charity peace of mind that best practice security measures are in place

Secure Configuration
Boundary Firewalls & Internet Gateways

Access Control & Administrative Privilege Management
Patch Management

Malware Protection
Cyber Essentials Insurance
Being compliant to Cyber Essentials has been shown to significantly reduce the likelihood and severity of a data breach. However, the risk still remain, especially if there is human error, a malicious insider or a concerted external attack. The presence of cyber insurance will provide vital incident response services and cover your costs in your hour of need. The insurance provided with certification gives you £25,000 limit of indemnity so you may want to purchase a higher limit of cover in case you suffer a severe breach.

Liability
Claims made against you arising out of privacy wrongful acts.
Event Management
Including emergency costs, data breaches and costs of notifying data subjects.

Business Interruption
Loss of profit and expenses caused by a network compromise.
Loss of Electronic Data
Costs of fixing the issue that allowed the loss or damage to your data.

Regulatory Investigations
Defence costs & regulatory fines (where insurable by law).
Read Our Cyber Security Blogs

Cybercriminals Capitalising on Remote Working
Recently, the amount of individuals working from home has seen an all-time high, but the number of those who do not have the correct security software implemented is staggering. This has led to a huge increase in cybercriminals attempting to perform attacks by exploiting remote login credentials and yours could be next!
5 Ways To Secure your Laptop Wherever it is
Whether you’re working from home or on-the-go, it is paramount that you protect your laptop from cyber-crime. While your company has probably provided you with a VPN to securely connect to their network, what about your personal passwords and local files? Let’s take a look at 5 great ideas to secure your laptop wherever it is;

Hackers Target Remote Desktop Protocol (RDP)
Stay alert whilst using Remote Desktop Protocol (RDP), remote working is providing a massive opportunity for hackers! As a result of the current pandemic, most organisations are turning to Remote Desktop Protocol (RDP) to permit staff to work from home.

How to Avoid COVID-19 Phishing Scams
Have you ever been worried that you may become a victim of a phishing scam? There has been several incidents of cyber criminals exploiting the COVID-19 pandemic recently, so listed below is some information and ideas of how to prevent this!